USDT flashing software like the Fake USDT Sender Software, the Trust Wallet Flasher Pro, and the Atomic Wallet Fake USDT Generator require utmost discretion, as the nature of cryptocurrency flashing constitutes a gray area.
On one end of the spectrum, blockchain security and forensics experts utilize these software tools. On the other end, these tools get exploited for unethical purposes.
Like every other software, the Fake USDT Sender Software is prone to intermittent threats, security risks, and cyberattacks, such as data theft or compromised user profiles, regardless of its intended use.
Several security measures and best practices should be considered while utilizing the fake USDT sender software to mitigate these risks.
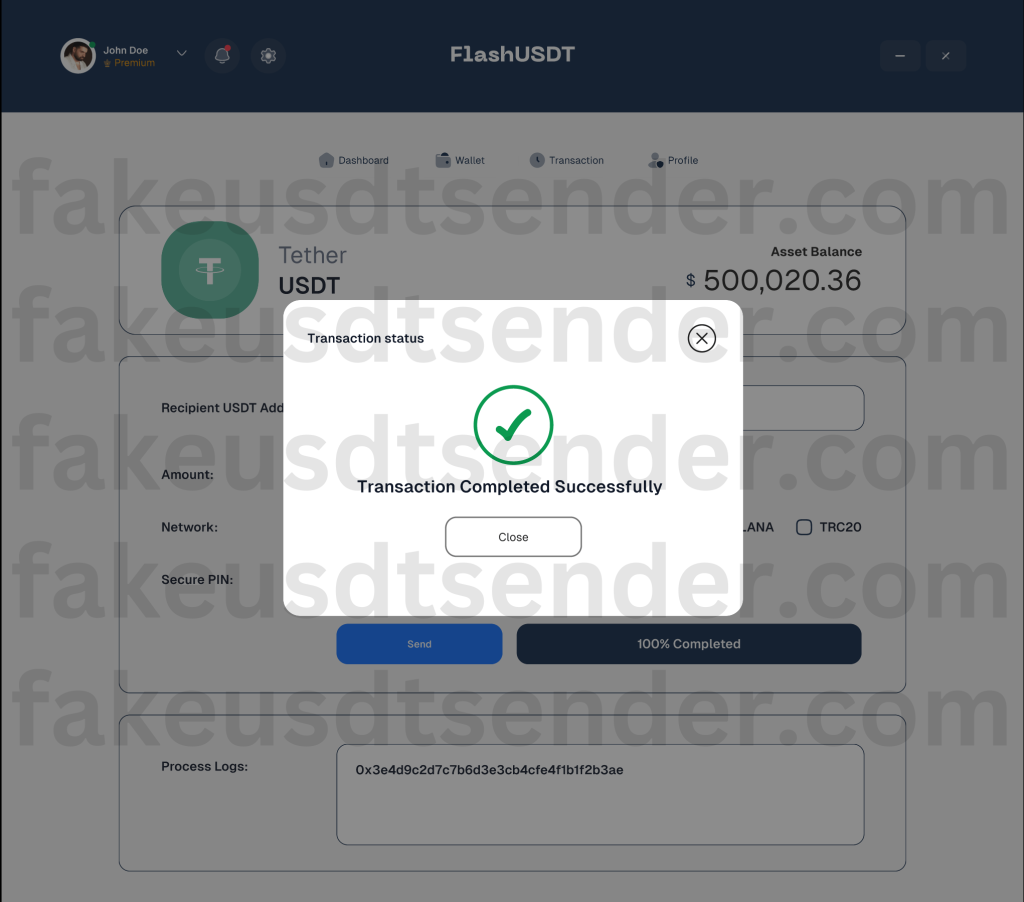
For those unfamiliar with the Fake USDT Sender Software, it is an application program that enables users to send fake USDT or flash USDT to multiple crypto wallets and exchanges across the blockchain.
The Fake USDT Sender Software grants up to $500K daily in flash USDT to full-access paid users, among other features and benefits.
Refer to our detailed guide on fake USDT tokens for a comprehensive analysis of the mechanisms behind the fake USDT Sender Software, flash USDT, and cryptocurrency flashing.
This article discusses several security tips and best practices for users to ensure robust data protection, reduced security risks, and improved performance for the fake USDT Sender Software.
Disclaimer: We have no control over who downloads or purchases our Flash USDT sender software and are not responsible for how Flash USDT is utilized across the blockchain. This software is intended exclusively for educational purposes and ethical use by blockchain security and forensic experts.
1. Purchase the Fake USDT Sender Software from Official Channels
The online marketplace for Fake USDT Sender Software and other cryptocurrency flashing tools is like the Wild West, with an ever-increasing number of shady vendors, bogus social channels, and sketchy resellers.
Unsuspecting buyers are lured into various channels through deceptive marketing tactics and promotional gimmicks, only to be swindled or tricked into installing malicious software programs that procure pathways for cyberattacks.
We recommend purchasing the Fake USDT Sender Software and other USDT flashing tools only from our official website, fakeusdtsender.com, and our verified Telegram handle to prevent fraud and cyber threats.
Ensure that all purchases for our software solutions, license keys, and activation codes are made through our official channels. We will not be responsible for any mishaps or avoidable incidents.
2. Protect Sensitive Information
Setting up user profiles on our USDT flashing tools does not require KYC verification. We do not collect any personal information to ensure complete privacy and anonymity.
Cryptocurrencies are the default payment method for the fake USDT Sender Software. After that, users are required to provide an email address to receive the software files in their inbox.
Any website, vendor, or reseller that acts otherwise is likely a fraudulent operator looking to steal private or personal information.
We discourage using home addresses as the delivery address for users who prefer to have a physical copy of the fake USDT Sender Software shipped to them.
As a precaution, delivery addresses should be to the closest landmark—the software program will be shipped and filed under the book category.
Sensitive information—such as user login email addresses, passwords, wallet passphrases, and activation codes—should not be shared with third parties or disclosed on public forums to prevent unauthorized access.
3. Install the Fake USDT Sender Software on a Secured Network
Internet cafes and public networks typically lack adequate security infrastructure to protect against threats and security risks. If a device within an interconnected network is compromised, it serves as a gateway to various forms of cyberattacks.
However, if public network service infrastructures are the only viable option, ensure security measures such as firewalls, antivirus scanners, and malware detectors are active on your computer system.
These security measures reduce the risks of being affected if a data breach occurs when unauthorized individuals exploit weak nodes to gain access to the public network.
Ensure a stable internet connection during flash USDT transfers to avoid abrupt disruptions. Always have a backup Wi-Fi connection ready to go should the primary internet source fail.
4. Update the Fake USDT Sender Software Regularly
Periodically, the fake USDT Sender Software and other USDT flashing tools within our software suite are updated to improve existing features or include new ones.
These software updates address issues like bugs and crashes and enhance the security frameworks and infrastructure within these tools.
The fake USDT Sender Software displays a notification message whenever a new version is released, prompting users to manually download and install the latest version.
Typically, users of the full-access fake USDT Sender Software plan are exempt from manual updates—the upgrade occurs automatically.
Explore the fake USDT Sender Software product page to learn more about the differences in features, specifications, and limits of the Starter, Basic, and Full-Access software plans.
Final Thoughts on How to Securely Use the Fake USDT Sender Software
Computer devices and software programs run on code, which makes them susceptible to potential threats and cyberattacks that exploit loopholes or vulnerabilities within their codebase.
There are several simple and easy steps to be implemented to minimize the risk of financial loss, security breaches, and data theft while navigating the web for USDT flasher tools.
Ensure you purchase, download, and install the fake USDT Sender Software only from our official website, fakeusdtsender.com, or our verified Telegram handle.
Refrain from using public networks unless your personal computer has an added layer of protection, such as firewalls, antivirus systems, and malware protection software, actively running.
Keep sensitive information such as passwords, activation codes, and license keys confidential, and avoid filling out private home addresses on billing forms unless necessary.
Lastly, always check our website for regular software updates or look for notification reminders on the Flash USDT Sender Software dashboard.
By meticulously following these guidelines, security tips, and best practices, you can safeguard yourself against unscrupulous vendors, data or identity theft, and other cyber threats—allowing for a seamless experience with the fake USDT Sender Software.
Need Help Getting Started?
Send us a message via Telegram, (Telegram: Contact @USDTFlashSender) and our support team will guide you through the purchase, setup, and flashing process.